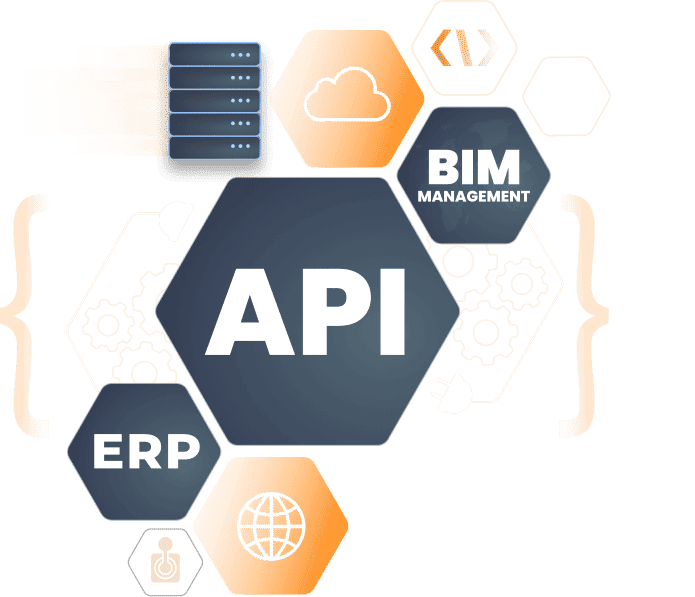
Incorporate Bazaar Insights BIMs Platform with your enterprise systems.
Enhance your product experience by integrating the BIM platform with your enterprise systems, driving success on the digital shelf.
Master Data Management (MDM)
Centralize, Standardize, and Link Critical Data Across Your Organization for Consistency, Accuracy, and Smarter Decision-Making.
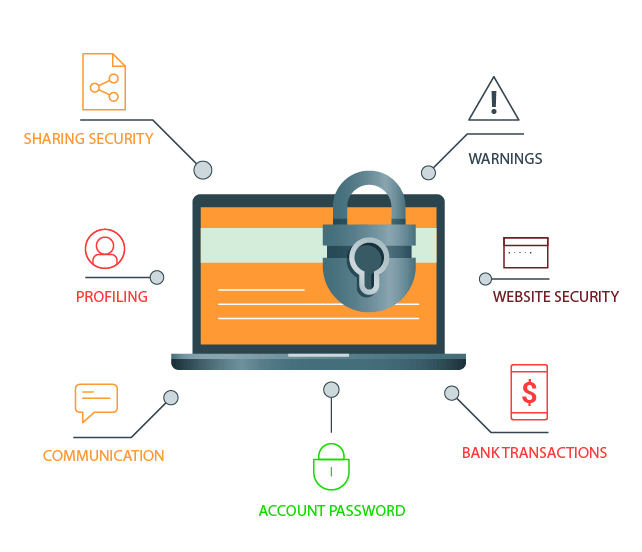
Data Security & Privacy
At Bazaar Insights, we prioritize your privacy and uphold the highest data protection standards. With advanced security measures, we ensure your information is secure on our trusted platform.